# Spring Cloud Data Flow整合Cloudfoundry UAA服务做权限控制
# 1 前言
关于Spring Cloud Data Flow这里不多介绍,有兴趣可以看下面的文章。本文主要介绍如何整合Data Flow和CloudFoundry UAA来做权限控制,而不是任何人都可以直接访问操作。
Spring Cloud Data Flow相关文章:
Spring Cloud Data Flow初体验,以Local模式运行 (opens new window)
把Spring Cloud Data Flow部署在Kubernetes上,再跑个任务试试 (opens new window)
Spring Cloud Data Flow用Shell来操作,方便建立CICD (opens new window)
被Spring坑了一把,查看源码终于解决了DataFlow部署K8s应用的问题 (opens new window)
UAA (opens new window),即CloudFoundry User Account and Authentication,一个身份认证和授权服务系统,主要用于CloudFoundry,也可以作为一个独立的OAuth2服务器,给客户端分发令牌。可以在单点登陆SSO等场景使用到它。
UAA还可以整合LDAP,但为了简化,本文只演示如何最简单的整合。
# 2 启动UAA服务
官方提供了war包形式的uaa.war,可以直接下载然后部署在Servlet容器上,如Tomcat等。UAA Bundled (opens new window)通过Springboot把war包包装起来,让启动应用像应用springboot一样简单。本文通过这种形式来启动。
通过插件maven-dependency-plugin来下载war包,如下:
<plugin>
<groupId>org.apache.maven.plugins</groupId>
<artifactId>maven-dependency-plugin</artifactId>
<executions>
<execution>
<id>copy</id>
<phase>process-resources</phase>
<goals>
<goal>copy</goal>
</goals>
</execution>
</executions>
<configuration>
<artifactItems>
<!--本地IDE启动时需要-->
<artifactItem>
<groupId>org.cloudfoundry.identity</groupId>
<artifactId>cloudfoundry-identity-uaa</artifactId>
<version>4.30.0</version>
<type>war</type>
<overWrite>true</overWrite>
<outputDirectory>${project.basedir}/src/main/resources</outputDirectory>
<destFileName>uaa.war</destFileName>
</artifactItem>
<!--打包成jar需要-->
<artifactItem>
<groupId>org.cloudfoundry.identity</groupId>
<artifactId>cloudfoundry-identity-uaa</artifactId>
<version>4.30.0</version>
<type>war</type>
<overWrite>true</overWrite>
<outputDirectory>${project.basedir}/target/classes</outputDirectory>
<destFileName>uaa.war</destFileName>
</artifactItem>
</artifactItems>
</configuration>
</plugin>
通过一个Springboot的主函数入口来调用:
@SpringBootApplication
public class UaaServer {
public static void main(String[] args) {
SpringApplication.run(UaaServer.class, args);
}
@Bean
public ServletWebServerFactory servletContainer() throws IOException {
final File tempDirectory = Files.createTempDirectory("uaa").toFile();
final File tempUaaYmlFile = new File(tempDirectory, "uaa.yml");
final File tempUaaWarFile = new File(tempDirectory, "uaa.war");
FileCopyUtils.copy(
new ClassPathResource("uaa.yml").getInputStream(),
new FileOutputStream(tempUaaYmlFile));
FileCopyUtils.copy(
new ClassPathResource("uaa.war").getInputStream(),
new FileOutputStream(tempUaaWarFile));
System.out.println("uaa.yml: " + tempUaaYmlFile.getAbsolutePath());
System.out.println("uaa.war: " + tempUaaWarFile.getAbsolutePath());
System.setProperty("UAA_CONFIG_FILE", tempUaaYmlFile.getAbsolutePath());
return new TomcatServletWebServerFactory() {
protected TomcatWebServer getTomcatWebServer(org.apache.catalina.startup.Tomcat tomcat) {
final Server tomcatServer = tomcat.getServer();
final File catalinaBase = new File(tempDirectory, "catalina");
catalinaBase.mkdirs();
tomcatServer.setCatalinaBase(catalinaBase);
new File(tomcatServer.getCatalinaBase(), "webapps").mkdirs();
try {
Context context = tomcat.addWebapp("/uaa", tempUaaWarFile.toString());
final ClassLoader properClassLoader = UaaServer.class.getClassLoader();
WebappLoader loader =
new WebappLoader(properClassLoader);
context.setLoader(loader);
} catch (Exception ex) {
throw new IllegalStateException("Failed to add webapp", ex);
}
return super.getTomcatWebServer(tomcat);
}
};
}
}
配置文件和war包的文件名硬编码了,实际项目可以通过配置来实现。
接着要配置uaa.yml文件,具体内容查看代码https://github.com/LarryDpk/pkslow-samples ,这里不贴出来了。注意需要生成JWT的key:
$ openssl genrsa -out signingkey.pem 2048
Generating RSA private key, 2048 bit long modulus
........................+++
..........................................................................+++
e is 65537 (0x10001)
$ openssl rsa -in signingkey.pem -pubout -out verificationkey.pem
writing RSA key
完成以上步骤后,可以打包启动了,命令如下:
mvn clean package
java -jar target/cloudfoundry-uaa-server-1.0-SNAPSHOT.jar
默认端口为8080。成功启动后,可以访问:http://localhost:8080/uaa/login

# 3 配置账号
为了方便,我们使用内存数据库来保存账户信息,重启后就会丢失。通过uaa提供的命令行工具uaac (opens new window)来创建用户与权限。因为uaac是基于Ruby的,所以还要先安装Ruby,我的电脑已经自带,这里就不演示了。
为了更快安装命令行工具cf-uaac,修改Ruby包管理工具gem的源:
$ gem sources --add https://gems.ruby-china.com
https://gems.ruby-china.com added to sources
$ gem sources -l
*** CURRENT SOURCES ***
https://rubygems.org/
https://gems.ruby-china.com
$ gem sources --remove https://rubygems.org/
https://rubygems.org/ removed from sources
配置了国内源后,安装:
$ sudo gem install cf-uaac
15 gems installed
安装完成后,就可以通过下面的命令来创建用户了。
uaac target http://localhost:8080/uaa
uaac token client get admin -s adminsecret
uaac client add dataflow \
--name dataflow \
--secret dataflow \
--scope cloud_controller.read,cloud_controller.write,openid,password.write,scim.userids,sample.create,sample.view,dataflow.create,dataflow.deploy,dataflow.destroy,dataflow.manage,dataflow.modify,dataflow.schedule,dataflow.view \
--authorized_grant_types password,authorization_code,client_credentials,refresh_token \
--authorities uaa.resource,dataflow.create,dataflow.deploy,dataflow.destroy,dataflow.manage,dataflow.modify,dataflow.schedule,dataflow.view,sample.view,sample.create \
--redirect_uri http://localhost:9393/login \
--autoapprove openid
uaac group add "sample.view"
uaac group add "sample.create"
uaac group add "dataflow.view"
uaac group add "dataflow.create"
uaac group add "dataflow.deploy"
uaac group add "dataflow.destroy"
uaac group add "dataflow.manage"
uaac group add "dataflow.modify"
uaac group add "dataflow.schedule"
uaac user add larry -p larry --emails larry@pkslow.com
uaac member add "dataflow.view" larry
uaac member add "dataflow.create" larry
uaac member add "dataflow.deploy" larry
uaac member add "dataflow.destroy" larry
uaac member add "dataflow.manage" larry
uaac member add "dataflow.modify" larry
uaac member add "dataflow.schedule" larry
uaac user add vieweronly -p mysecret --emails vieweronly@pkslow.com
uaac member add "dataflow.view" vieweronly
这里关键的是用户和群组,即user和group。这里配置的信息,会与Data Flow Server的配置对应上才可以。
# 4 配置与启动Data Flow Server
Data Flow Server的配置文件非常重要,它是整合UAA的关键。关键是两部分,第一部分是配置UAA各种信息,如clientId,Token的地址,各种鉴权地址等;第二部分是角色映射,Data Flow是基于角色的权限控制,它自己的角色要和UAA的群组映射起来才可以正常使用。
配置如下:
spring:
security:
oauth2:
client:
registration:
uaa:
client-id: dataflow
client-secret: dataflow
redirect-uri: '{baseUrl}/login/oauth2/code/{registrationId}'
authorization-grant-type: authorization_code
scope:
- openid
- dataflow.create
- dataflow.deploy
- dataflow.destroy
- dataflow.manage
- dataflow.modify
- dataflow.schedule
- dataflow.view
provider:
uaa:
jwk-set-uri: http://localhost:8080/uaa/token_keys
token-uri: http://localhost:8080/uaa/oauth/token
user-info-uri: http://localhost:8080/uaa/userinfo
user-name-attribute: user_name
authorization-uri: http://localhost:8080/uaa/oauth/authorize
resourceserver:
opaquetoken:
introspection-uri: http://localhost:8080/uaa/introspect
client-id: dataflow
client-secret: dataflow
cloud:
dataflow:
security:
authorization:
provider-role-mappings:
uaa:
map-oauth-scopes: true
role-mappings:
ROLE_VIEW: dataflow.view
ROLE_CREATE: dataflow.create
ROLE_MANAGE: dataflow.manage
ROLE_DEPLOY: dataflow.create
ROLE_DESTROY: dataflow.create
ROLE_MODIFY: dataflow.create
ROLE_SCHEDULE: dataflow.create
可以看出,多个不同角色可以映射同一个群组,非常灵活。
配置完成后,就可以启动Data Flow Server了:
java -jar data-flow-server.jar --spring.config.additional-location=./src/main/resources/application.yaml
# 5 体验成果的时候到了
成功启动UAA并配置用户,再启动Data Flow Server后,便可以开始使用了,过程如下:
访问http://localhost:9393/dashboard/#/apps 会自动跳转到登陆界面,点击uaa:

跳转到uaa的登陆界面:
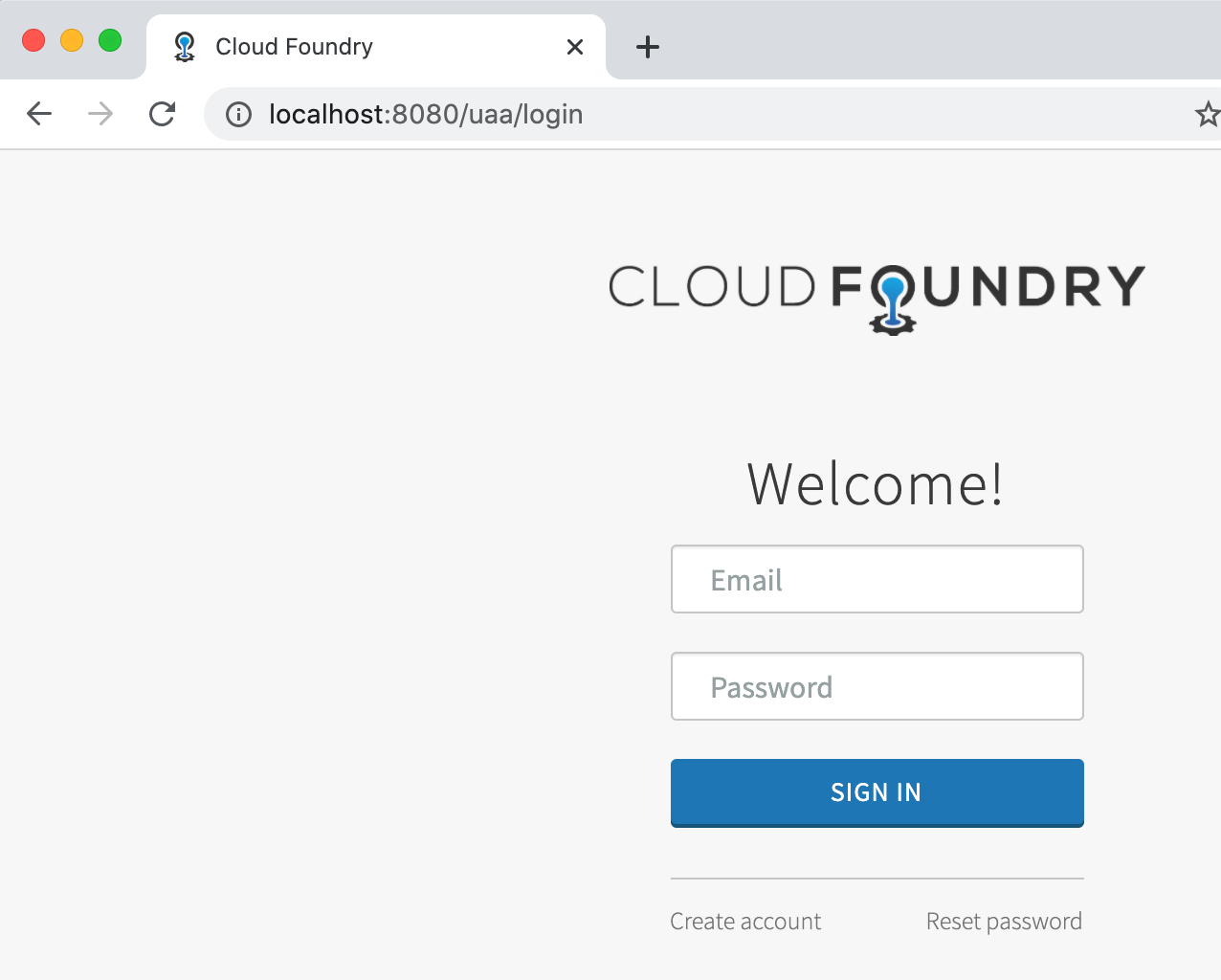
输入配置的账号密码:larry/larry,上面显示为Email,其实并不是。登陆后就要确认授权:

授权后,会自动跳转回Data Flow的界面,并已经有权限进行查看操作了:

登出后,又要要求重新登陆。至此,我们已经成功地整合了。
而shell的使用如下:
$ java -jar spring-cloud-dataflow-shell-2.7.0.jar \
--dataflow.uri=http://localhost:9393 \
--dataflow.username=my_username \
--dataflow.password=my_password \
--skip-ssl-validation true
# 总结
本文通过一步步演示如何整合Data Flow Server和UAA,以实现Data Flow安全要求。实际UAA应该使用其它数据库,如MySQL,或整合LDAP,这样重启账号数据不会丢失。后续有空再讨论吧。
代码请查看:https://github.com/LarryDpk/pkslow-samples
参考文档: